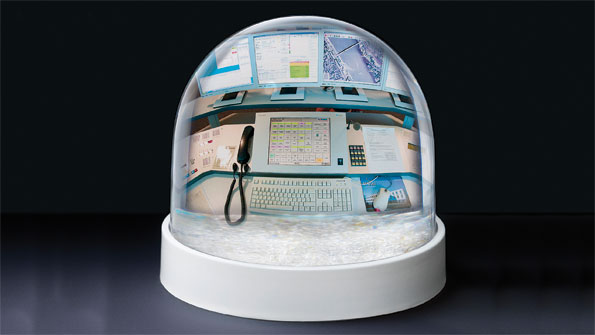
Protecting NG-911 in five steps
The remaining steps
Now let's examine the remaining steps for implementing a NG-911 security standard.
Step 2: Policies — A lot of thought, planning and enormous amounts of coordination are needed prior to arriving at the point where you are ready to author policies. Policies are utilized to communicate the expectations and appropriate behavior on the network.
During the planning stage, you identified regulatory, legislative and administrative documents that impact your environment. When authoring policies, it is important to involve entities that have a stake in your network and, specifically, the security of your network. From governing authorities to other agencies on your network, each may provide rules for network connectivity and information sharing. Your security standards may differ. Always choose the most secure requirements. Do not permit access to your network unless the requestor honors your security standards while connected to your network.
Procedures are instructions to utilize when performing a task — e.g., configuring a workstation. It is beneficial to document procedures. This allows tasks to be conducted consistently, avoiding security issues caused by conflicting methodologies. It also is helpful to provide a change-management procedure to coordinate changes to installations, upgrades and other activities that potentially could impact network security.
Step 3: Train — This is a lot of new information for your employees to assimilate. You should provide training to help them understand the security plan, policies and procedures. This also provides a platform to discuss processes and resolve misunderstandings. Technology is dynamic and creates ever-changing security needs. Annual and periodic training is necessary to keep employees informed of changes to security requirements.
Step 4: Monitor — All of this hard work, planning, coordinating and documenting will be for naught if you fail to monitor your network. Systems that are capable of logging information should do so. A systematic approach for reviewing logs and providing reports should be established. High-impact events, such as a virus on the network, should trigger an alarm that immediately notifies personnel to take action. If services are provided by another entity, require reports and establish notification procedures via contracts and service-level agreements.
Step 5: Audit — Audit your network on an annual basis. Compare your environment to your chosen security standard. Remember the gap analysis from the planning step? Again, identify your security gaps and execute strategies to remain compliant. Utilize the information gained from audits to update your plan, policies and procedures, if needed. Continue to monitor your environment to assure that security measures are providing the expected outcome. Security requires persistent commitment.
It may be difficult to believe, but this article merely touches on the basics. Firewalls, intrusion detection and prevention systems, authorized access (physical and cyber), passwords and encryption are a few of the many other security considerations.
Security compliance is complex. It requires perpetual planning and coordination, but it is a necessity. From agencies that find their personnel information posted on a hacker's website to networks that are unable to provide service due to a denial-of-service attack, these are real world events that can be prevented — in five steps.
Lori J. Kleckner, PMP, CISSP is a cybersecurity consultant for L.R. Kimball with extensive experience in collaborating with agencies at the local, state and national levels.







Good sound advice.
Good sound advice.