Polaris unveils location-based application suite for law enforcement
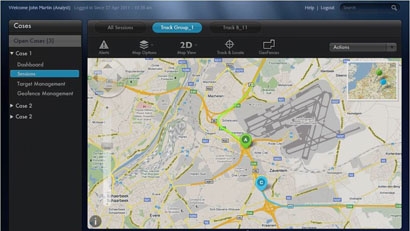
Location-services provider Polaris Wireless recently announced its Altus suite of applications, which is a software-based surveillance solution that lets law-enforcement agencies track all subscribers in a wireless network in real time and on a historical basis.
Powered by the patented Polaris Wireless Location Signatures (WLS), Altus enables functions such as target identification, tracking via geofence and post-event analytics, according to the company, which already has customers in Asia and the Middle East using the solution.
“What the agencies in these countries are realizing is that it’s not enough just to have an XY location,” said Bhavin Shah, vice president of marketing and business development for Polaris Wireless. “They want to know, ‘How do we make sense out of (the location information)? What else can we do with it?
“We basically came up with a location solution platform — our Altus suite — which is basically an application platform that consumes location from our underlying platform and then is able to give law enforcement an opportunity to do things with it,” he said.
With the Altus suite, law-enforcement officials can establish a geo-fence around an area and receive automatic notification if the mobile device of a suspect enters or leaves the designated area, Shah said. In addition, historical-mass-location capabilities can be used to support forensic analysis after an event has occurred.
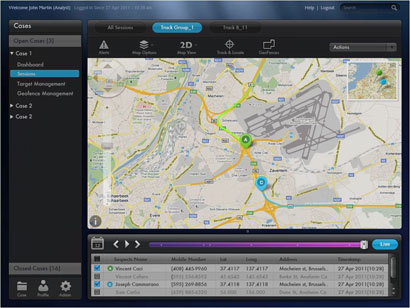
“What we’re able to do is go back in time, put the geofence on it, take the data from that area and tell who was in that area when that event happened,” Shah said. “They can go back and see what mobile devices were there at that time before the event happened, compare it to after the event happened and start to do some forensic analysis.”
Of course, potential suspects may change phones and SIM cards regularly. Altus allows law enforcement to track in several ways — by phone, phone number and SIM card — to combat such techniques, Shah said.
“Using a combination of one or more of these parameters, we’re able to continue tracking them, even if they change phones or SIM cards or whatever,” he said.
In situations where a suspect opts to use a new device and phone number, patterns in the historical databases can be used to associate the new device with the suspect, Shah said.