93% of tested networks vulnerable to breach, pen testers find
The vast majority of businesses can be compromised within a month by a motivated attacker using common techniques, such as compromising credential, exploiting known vulnerabilities in software and Web applications, or taking advantage of configuration flaws, according to an analysis of security assessments by Positive Technologies.
In 93% of cases, an external attacker could breach a target company’s network and gain access to local devices and systems, the company’s security service professionals found. In 71% of cases, the attacker could affect the businesses in a way deemed “unacceptable.” For example, every bank tested by the security firm could be attacked in a way that disrupted business processes and reduced the quality of their service.
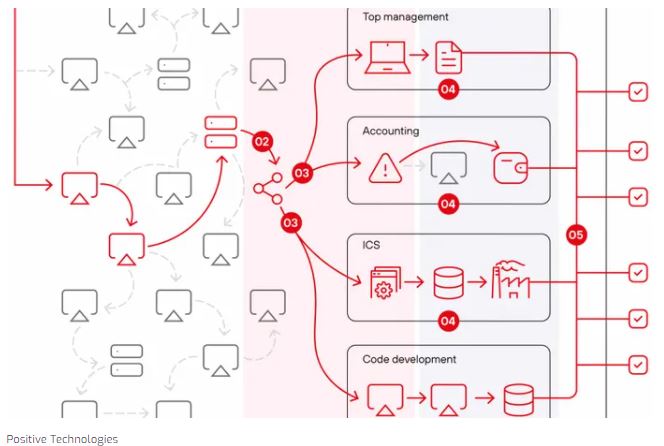
Positive Technologies describes cyberattacks as a series of compromises of key systems that then expose a target system to malicious manipulation. This, in turn, causes one or more “unacceptable events,” which may include disruption of production or services, compromise of executives’ identities, theft of money or sensitive data, and/or the ability to defraud users.
Positive Technologies’ annual report shows that companies need to take stock in 2022 and model likely threats, says Ekaterina Kilyusheva, the company’s head of research and analytics.
“Every company can fall victim to an attack, both targeted and massive,” she says. “According to our data, the number of cyberattacks is increasing from year to year, and their consequences are becoming more serious. Just look at the damage that ransomware operators inflict on organizations.”
The study examines data from security assessments performed from the beginning of July 2020 through the end of June 2021. The company’s penetration testers conducted assessments of dozens of companies and used 45 projects as the basis for the report.
They found compromised credentials were the most reliable way to gain entry into a corporate network, with credential use succeeding in 71% of projects because most employees use overly simple passwords. In 60% of projects, exploiting unpatched software with known vulnerabilities allowed the attacker to further infiltrate a target company’s network. In 54% of cases, misconfiguration of devices and software led to greater compromise.
To read the complete article, visit Dark Reading.