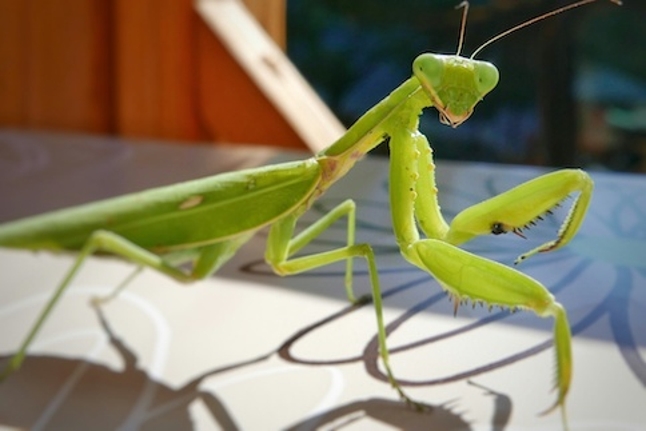
Praying Mantis threat group targeting US firms in sophisticated cyberattacks
A sophisticated threat actor behind a series of highly targeted attacks on Australian companies and government entities last year may be carrying out a similar campaign against US organizations using almost only memory-resident malware.
Researchers at Sygnia this week reported observing attacks bearing all the hallmarks of the Australian campaign targeting what they described as high-profile public and private entities in the US. Sygnia says the threat actor — which it is tracking as Praying Mantis or TG2021 — has been attacking Windows Internet Information Services (IIS) environments and Web applications to gain initial access on target networks.
The attacks have been going on since at least last June and appear to be a cyber-espionage operation for a state-backed entity. “While the full scope of activity is unknown to Sygnia, the level of sophistication and highly persistent nature of the threat actor suggests the existence of a large operation,” says Arie Zilberstein, vice president of incident response at Sygnia.
Some reports out of Australia last year have suggested the activity is linked to China — a country the Biden administration recently publicly accused of using criminal gangs to conduct cyber espionage and other malicious missions on its behalf.
Zilberstein says Sygnia first uncovered signs of the campaign when responding to a report of a potential compromise on a customer network. “This gradually unfolded the attack and tool set, which made it more trackable,” he says.
According to Sygnia, the threat actor’s main tactic for gaining a foothold on a target network has been to use different so-called deserialization exploits against IIS and vulnerabilities in Web applications. Zilberstein explains a deserialization exploit as one that leverages the way an application initializes objects that have been serialized. “If the deserialization process is insecure, the program can be exploited to execute malicious code on the target.”
To read the complete article, visit Dark Reading.