Researchers warn of stealthy Chinese backdoor targeting multiple foreign agencies
A stealthy backdoor program discovered in tools used by China-linked threat actors has targeted government computers at multiple foreign agencies, allowing attackers to retain a presence on sensitive networks and exfiltrate data — while remaining undetected.
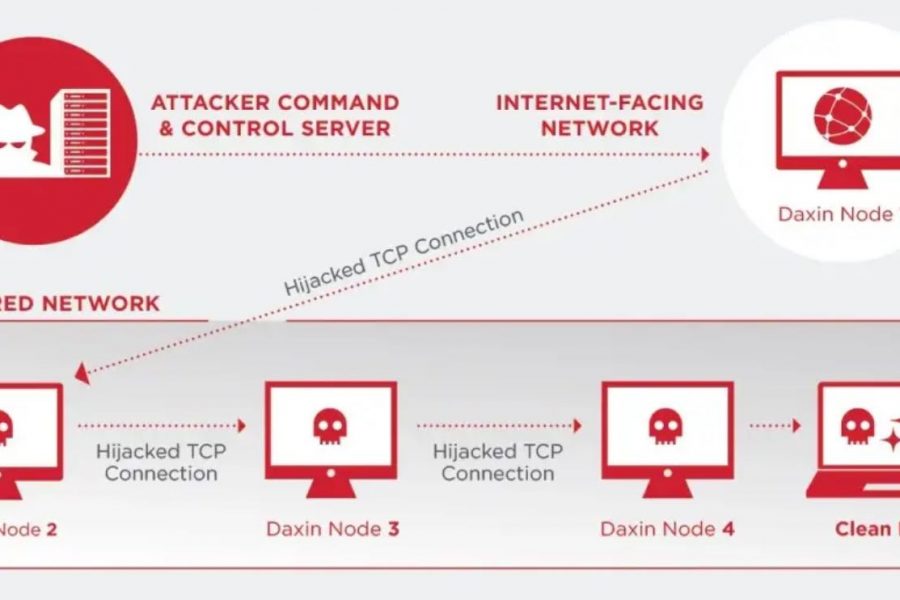
Researchers at Symantec, a division of Broadcom Software, said in an advisory issued today that the backdoor, which they have dubbed as Daxin, is “exhibiting technical complexity previously unseen.” It gives attackers the ability to stealthily gather data on compromised systems and communicate the information to the attacker through machine-in-the-middle techniques. The malware — used as recently as November 2021 — has targeted government agencies in nations of strategic interest to China, Symantec stated, although the company did not name the organizations that had been affected by the malware.
The care with which the Chinese threat actors developed and used the backdoor differs dramatically from the standard programs and tools typically found by researchers, says Vikram Thakur, lead researcher at Broadcom’s Symantec.
“This is the first threat that we have seen where they are conscious about long-term cyberattack campaigns for cyber espionage,” he says. “In the past, Chinese threat actors have always seem to have little worry about being caught. We assumed that they treated their tools as one-use, but they have been [using Dakin] for over a decade, which means our original thinking was incorrect.”
The backdoor is a Windows kernel driver implementing advanced communication features that allows its operators to infect systems on highly secure networks and let them to communicate without detection, even when the systems can’t connect to the Internet. These features are similar to the Regin malware discovered by Symantec in 2014, and which the company attributed to Western intelligence agencies.
Symantec tracked the history of the Daxin backdoor back to 2013, with most of the advanced features already existing in the malware at that point, which “suggests that the attackers were already well established by 2013,” the company stated in its advisory. The company believes that the intelligence group behind the malware existed at least as early as 2009, based on similarities to other programs.
“Daxin’s capabilities suggest the attackers invested significant effort into developing communication techniques that can blend in unseen with normal network traffic on the target’s network,” Symantec stated in the advisory. “Specifically, the malware avoids starting its own network services. Instead, it can abuse any legitimate services already running on the infected computers.”
To read the complete article, visit Dark Reading.